WebApp Authentication with Social Identity Providers (Google, Facebook & Apple ID)
|
Field |
Details |
|
Document Type |
Runbook / How-To Guide |
|
Applies To |
Microsoft Entra ID External Identities (CIAM), Social Identity Providers (Google, Facebook, Apple), Third-party Web Applications |
|
Audience |
Systems Administrators / Identity Engineers / 2nd Line Support |
|
Author |
AK. Udofeh |
|
Last Updated |
March 2026 |
Overview
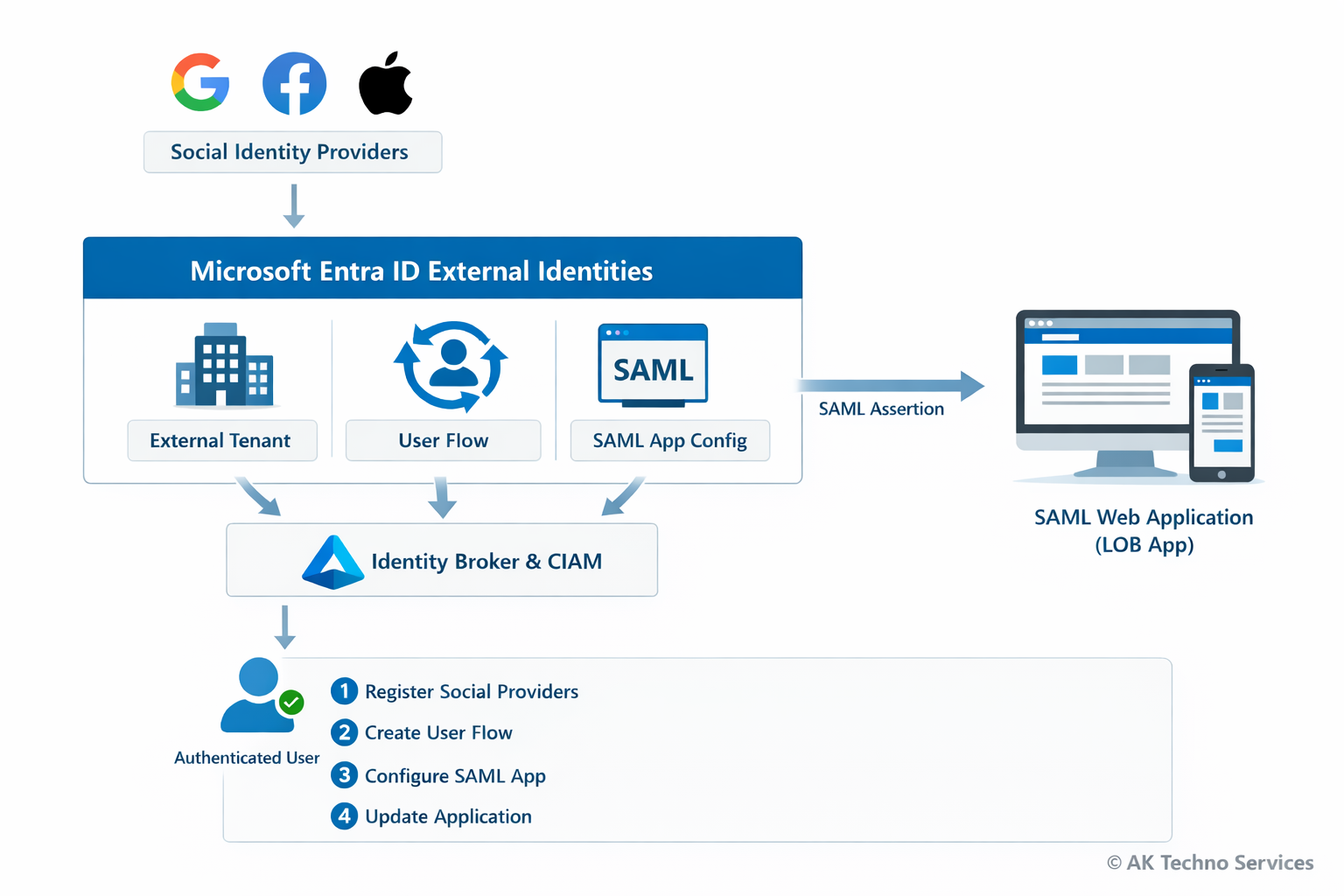
This guide documents how to integrate Social Identity Providers (Google, Facebook, and Apple) with a SAML-based web application for authentication using Microsoft Entra ID External Identities and Customer Identity & Access Management (CIAM). The configuration allows users to authenticate using social accounts while Microsoft Entra acts as the identity broker and issues a SAML assertion to the third-party or line-of-business (LOB) web application.
The process involves creating an external tenant, registering social identity providers, creating a user flow, configuring a SAML enterprise application, and updating the application configuration.
The Issue
Organisations often require users to authenticate using Social Identities (e.g. Google or Facebook) while maintaining a centralised identity broker for security and policy enforcement.
Without a configured identity broker:
-
Applications must integrate individually with each social provider.
-
Identity attributes are inconsistent between providers.
-
Access control and auditing become difficult to manage.
Basic authentication methods such as:
-
Local application accounts
-
Direct OAuth integration within the application
do not provide centralised identity management or federation capabilities.
Using Microsoft Entra External Identities resolves this by brokering authentication from social providers and issuing a standard SAML assertion to the application.
Context
Modern applications often require authentication from multiple identity providers while maintaining centralised access control.
Without a broker, the authentication flow typically looks like this:
User
↓
Application
↓
Direct OAuth with Google/FacebookThis causes several issues:
-
Applications must implement provider-specific authentication logic
-
Identity attributes differ between providers
-
Access control cannot be centrally enforced
Using Microsoft Entra External Identities introduces an identity broker layer:
User
↓
Google / Facebook / Apple
↓ (OAuth / OIDC)
Microsoft Entra External Tenant (CIAM)
↓ (User Flow)
Enterprise Application (SAML)
↓
Flask Web ApplicationIn this architecture:
Before You Start
Check |
Where |
|---|---|
External tenant created |
Microsoft Entra admin centre |
Azure subscription linked |
Tenant creation wizard |
Google Developer Console account |
console.cloud.google.com |
Meta Developer account |
developers.facebook.com |
Apple Developer account (optional) |
developer.apple.com |
SAML web application deployed |
Flask service |
Service Provider metadata configured |
|